
Survey respondents also point to port infrastructure issues and shifts in economic policy.
Supply Chain Insights recently conducted a survey with the objective to understand the “current and expected future state of supply chain risk management, the biggest drivers of risk, and the impact on supply chain disruptions.”
While nearly two-thirds of respondents believe their company performs better today on risk management practices that five years ago, they still had 3.5 disruptions last year on average. According to the report, “Managing risk requires a network approach. Today’s investments in an end-to-end supply chain are, by and large, not effective in risk mitigation.” In fact, only 37% have visibility of extended-tier suppliers and most lack the solutions to manage global complexity.
In line with a recent Task Force 7 Radio interview with Chuck Brooks, Principal Market Growth Strategist for General Dynamics Mission Systems for Cyber Security, noted how new technologies such as IoT, ML or AI also bring along new risks. For example, there is no security built into these new devices (such as IoT devices), which makes it difficult to protect. In turn can affect the full supply chain “as you have connectivity through the supply chain,” explained Brooks.
While the report addresses how companies must manage risk to drive opportunities, it’s important to note how Supply Chain Insights defines “Supply Chain Risk Management” as:
The proactive identification and assessment of potential risks to the supply chain – as well as the development of strategies to avoid these risks.
Further, the report defines a disruption as a ‘major outage or discontinuity in operations.’ Few companies in the survey have a department to focus on risk management. Instead, it was found that risk management is embedded in other practices for nearly two-third of respondents.
“However, based on the results of this study, we question if it is embedded effectively,” notes Lora Cecere, Founder, Supply Chain Insights. While supply chain technologists offer a range of solutions to improve risk management, most focus on improving supply chain visibility. There is a gap between business requirements and technology solutions. Few technologists understand the need for solutions to help companies manage the complexity of operations, or the increasing requirements for regulatory compliance, she also noted in the study.
Survey response also revealed three issues impacting effective risk management:
- Demand: Companies focus risk management on ‘supply-side issues’ not on ‘demand/channel sending and translation.’
- Active management of the extended supplier network: In the case of a natural disaster, only 37% of companies have visibility of their second tier of suppliers or beyond.
- Active monitoring of financial health status and health: This requirement improves the design of the value network to improve supplier viability (for most companies, this is a gap).
Perhaps most revealing to cyber security professionals in this study is the response on top events that impacted supply chain. While most companies focus on business continuity through plans for natural disasters (i.e. earthquakes, floods, hurricanes and drought), this is not sufficient enough to meet the challenge of risk in the supply chain.
“The good news is that corporate preparedness for natural disasters… has helped global supply chain weather many storms like hurricanes Harvey, Irma, Maria and Sandy,” explained Cecere. But, business continuity and risk mitigation require more that just a focus on natural disasters.
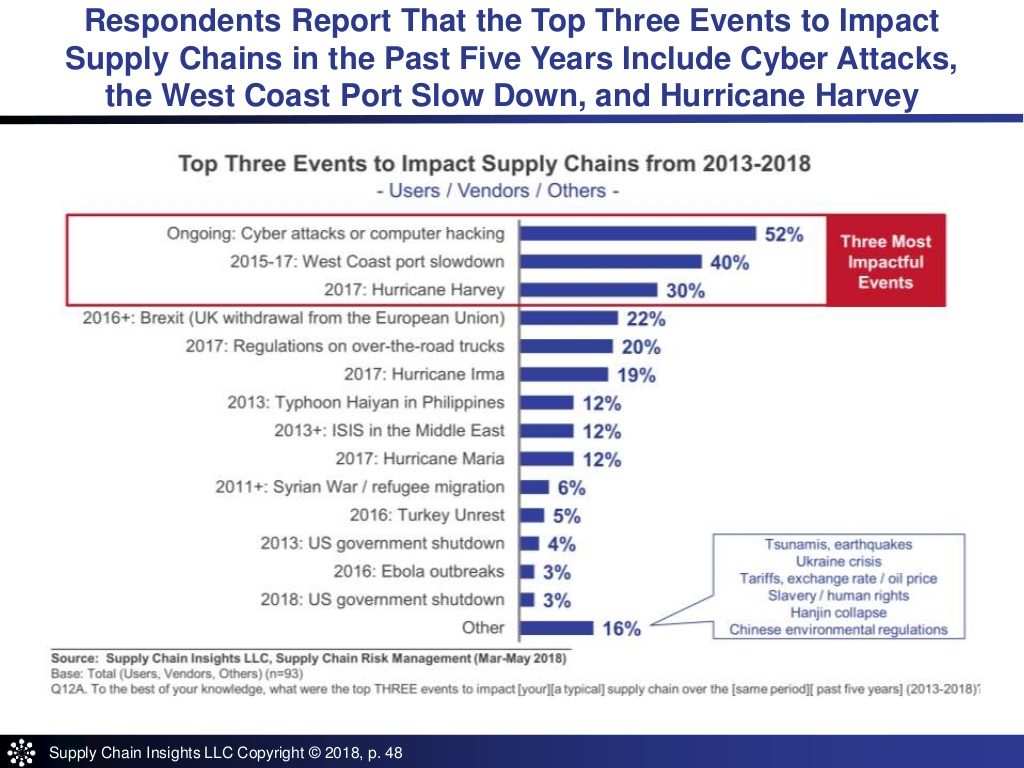
When asked about the top three events which impacted their supply chains during the period of 2013-2018, respondents mentioned cyber security, port infrastructure issues and shifts in economic policy with Brexit.
Cecere added, “Cyber-attacks are worthy to note. The impact is growing. It is not a major factor in our prior risk management reports. It is expected to grow through the evolving decade.”
According to Brooks, even the government is prioritizing third-party risk because it goes back to that full connected supply chain with a variety of parties linked to that network: “For attackers, they’ll always look for the weakest point of entry.”
Supply Chain Risk Management Recommendations
As such, Cecere concluded the report with recommendations for managing supply chain risk. “Risk management requires holistic thinking. The focus is top-down and horizontal – working across functional silos – and led by a business leader.”
In building and rethinking risk management programs, keep these five elements in mind:
- Leadership Matters: Programmatic risk management is needed to drive holistic thinking. This is not a program that can be effectively managed bottom-up. It also tends to get lost when managed as part of other programs. Proactivity is key. Business continuity programs should not be an afterthought.
- Build Agility in Operations: Actively define and proactively implement agility programs. Design, implement, and reward agility improvements. Educate financial teams on the differences between efficiency (lowest cost per unit) and agility (the ability to have the same cost, quality and customer service level given a level of demand and supply variation).
- Implement Supplier Sensing and Supplier Visibility Programs: Visibility of suppliers – locations of facilities and their suppliers – is the first step. The second is supplier financial sensing. Companies with advanced risk management programs redesign the role of procurement to build, not just audit, value chain relationships.
- Avoid Shiny Objects: While technology vendors espouse risk management as a technology, it is much more that the deployment of a technology. While visibility technologies are an important part of the solution, they are not the answer.
- Things Happen. Not all Risks can be Prevented. Be Prepared: Events cannot be total prevented, but they can be mitigated. The design of inventory buffers and supplier visibility programs are critical, but it is also important to have well-defined practices and drills to help the organization mobilize quickly in the face of a disaster.
“It is not a time for indecision. When a disruption happens, there needs to be a clear definition of protocols and responsibilities. Many advanced companies implement drills and practice deployment to ensure readiness,” Cecere said.
Source: Cyber Security Hub




